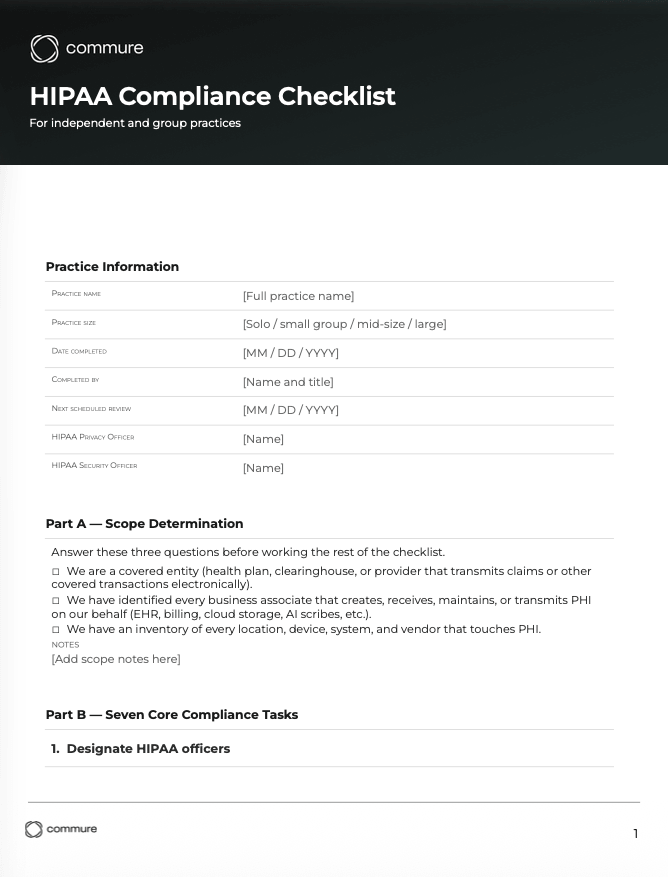
HIPAA Compliance Checklist: Free 7-Step Template
From scope to audit readiness in seven operational steps for independent and group practices.
Written by the Commure Scribe Team
Published: May 15, 2026
•
8 min read
What You Need to Know
- HIPAA applies to two groups: covered entities (providers, health plans, clearinghouses) and their business associates, including EHR vendors and AI documentation tools.
- A defensible HIPAA program organizes work into recurring tasks, including the Security Rule's required risk analysis of ePHI.
- Every breach requires individual notice within 60 days; 500+ individuals total adds HHS notice; more than 500 residents of one state or jurisdiction adds media notice.
What is a HIPAA compliance checklist?
A HIPAA compliance checklist turns federal rules into actions your practice can complete and document. The rules come in three parts: Privacy, Security, and Breach Notification. HHS publishes the rules and guidance but not an official HIPAA compliance checklist. Practices build or adopt one to close the gap.
A good HIPAA compliance checklist covers the duties every covered entity and business associate has to meet. It does not replace reading the rules themselves. Those duties include:
- Designating responsibility for compliance
- Running a formal risk analysis of electronic protected health information
- Implementing administrative, physical, and technical safeguards
- Managing business associate agreements
- Training staff
- Preparing for Office for Civil Rights audits and breach notification
Older templates often skip AI documentation tools that handle PHI; modern checklists cover them. The sections below walk through each duty: scope, the seven core steps, risk analysis, safeguards, AI tool evaluation, and audit prep. A HIPAA compliance checklist turns each one into a task you can document and audit.
Who must follow HIPAA and what counts as protected health information?
A HIPAA compliance checklist begins with scope. HIPAA applies to two categories of organizations: covered entities and business associates.
Covered entities include:
- Health plans
- Health care clearinghouses
- Most health care providers that transmit claims or other covered transactions electronically⁶
A solo primary care clinic billing Medicare falls in this scope. So does a multi-provider specialty practice billing commercial payers.
Business associates are outside vendors or contractors that handle PHI for a covered entity⁶. Common examples include:
- EHR vendors
- Billing services
- Cloud storage providers
- AI documentation tools
OCR's audit protocol checks whether covered entities have signed BAAs in place³. Those agreements must also bind subcontractors to protect PHI.
Protected health information (PHI) is any personal data about a patient's health, treatment, or billing. PHI includes:
- Names, dates, and addresses
- Medical record numbers
- Diagnoses and treatment notes
- Billing codes
- Audio recordings from a clinical encounter
Electronic protected health information, or ePHI, is the same data held or transmitted in electronic form. ePHI is the specific focus of the Security Rule.
What are the core steps of a HIPAA compliance checklist?
This template organizes key HIPAA duties into seven repeatable tasks. Work through them at least once a year. Other frameworks also work, as long as they cover the same ground. HHS and the AMA treat HIPAA as ongoing work¹,². Risk management and staff training are not one-time projects.
The seven core steps are:
- Designate a HIPAA privacy official and security official. These roles can be held by the same person in small practices or split across roles in larger groups. Document the assignments in writing.
- Perform a documented risk analysis of ePHI. The Security Rule requires an accurate and thorough assessment of risks to electronic protected health information⁵. Revisit the analysis at least annually and whenever significant changes occur.
- Write policies and procedures. Cover each Security and Privacy Rule requirement in enough detail that staff can follow them.
- Train every staff member. Train people for their role at onboarding and at regular intervals after. Keep training records¹.
- Sign a BAA with every vendor that handles PHI for you. OCR reviews BAAs and checks that they also bind subcontractors to protect PHI³.
- Build an incident response and breach notification process. The process must meet federal timelines for notifying affected individuals, HHS, and media where required.
- Retain required HIPAA documentation for at least six years from creation or last effective date. Retention applies to policies, risk analyses, training records, BAAs, and breach documentation. State law or organizational policy may require longer retention for medical records.
Every item on the HIPAA compliance checklist needs an owner, a cadence, and a record. Policy binders alone do not satisfy HIPAA.
How does practice size change who owns each step?
The seven core steps apply to every covered entity, but ownership and execution differ by practice size. Solo and small practices typically consolidate roles; medium and large groups distribute them across functions.
Where practice size changes AI tool review. The five review criteria apply to every practice, but review depth scales with size. Solo and small practices usually accept vendor SOC 2 reports at face value and rely on standard BAA terms. Medium and large groups run their own security review, negotiate BAA language, and ask for proof of tenant isolation or dedicated hosting.
How do I conduct a HIPAA risk analysis for my practice?
A HIPAA compliance checklist treats the risk analysis as its most time-sensitive item. A HIPAA risk analysis is a written review of where your ePHI lives, what could go wrong, and what you're doing about it⁵. It must cover three things: confidentiality, integrity, and availability. Treat the analysis as an ongoing process. Revisit it at least once a year and after any major change to systems, staff, or vendors.
A defensible risk analysis has four outputs:
- An ePHI inventory. List every system, device, and vendor that stores or transmits PHI, including EHRs, cloud storage, email, mobile devices, and AI documentation tools.
- A threat and vulnerability list. Identify realistic threats (ransomware, lost laptops, phishing, unauthorized access by former staff) and the weaknesses in current controls that each could exploit.
- A likelihood and impact rating for each risk. HHS does not mandate a specific scoring method, but ratings must be reproducible and tied to evidence.
- A fix-it plan with owners and deadlines. Every high or medium risk gets assigned to a named person with a target completion date.
Small practices can knock out a first pass in one or two focused sessions, then expand it over time. A good starting point is the free Security Risk Assessment Tool from HHS and ONC. Larger groups usually need a team covering clinical, IT, and admin. Either way, the output is a written report kept on file and reviewed on a set schedule. A mature HIPAA compliance checklist feeds the risk analysis findings into your fix-it list.
What administrative, physical, and technical safeguards does the Security Rule require?
The Security Rule groups required protections into three categories: administrative, physical, and technical safeguards¹. Each one protects ePHI against a different kind of risk. A HIPAA compliance checklist that skips any of the three leaves ePHI exposed.
Administrative safeguards cover how people and processes manage PHI. Required standards include:
- Risk analysis and risk management
- Workforce clearance and training
- Information access management
- Contingency planning
- Periodic program review
Physical safeguards cover the buildings, equipment, and devices that touch PHI. Standards include:
- Facility access controls (locks, keycards, visitor logs)
- Workstation use and security rules
- Device and media controls covering disposal, reuse, and accountability of laptops, phones, and removable storage
Technical safeguards cover the electronic controls that limit and monitor access. Standards include:
- Unique user identification
- Automatic logoff
- Encryption of ePHI in transit and at rest
- Audit controls that log system activity
- Integrity controls that detect unauthorized alteration
All Security Rule standards are mandatory. Within each standard, individual implementation specifications are classified as "required" or "addressable"¹. Required ones must be implemented as written. For addressable ones, decide whether the specified control fits your practice. If it doesn't, document an alternative that works and explain why.
Every safeguard on the HIPAA compliance checklist needs evidence. Proof can be a written policy, a configuration setting, or a log entry a compliance officer can pull on demand.
How do I evaluate AI scribes and other AI tools for HIPAA compliance?
A modern HIPAA compliance checklist has a dedicated AI tool section. Before trusting an AI scribe or other HIPAA-relevant AI tool with PHI, ask for proof of the security controls underneath. Marketing claims or a compliance badge on a vendor website are not enough. Clinicians warn that many AI products claim HIPAA compliance without showing the controls to back it up. A solid review covers five areas.
- Business associate agreement. If an AI vendor will handle your PHI, sign a BAA first. The BAA must bind the vendor and its subcontractors to protect PHI³.
- Encryption in transit and at rest. Ask which protocols the vendor uses in transit (such as TLS or HTTPS) and what encrypts data at rest (such as AES-256 or equivalent). Ask how keys are managed.
- Data retention and deletion. Ask where audio and transcripts are stored, how long, and how they're deleted. A HIPAA compliant AI tool states a default retention period and supports your six-year record retention through export, hand-off, or a similar mechanism.
- Training data policy. Confirm in writing whether audio, transcripts, and notes are used for model training, product improvement, or any purpose beyond generating the clinical note. Many organizations require written limits.
- Third-party audit. Ask for a SOC 2 Type II report, HITRUST certification, or equivalent. Most compliance officers won't trust a vendor's word alone.
If a vendor can't answer these five questions with paperwork, many groups won't approve the tool for live use with PHI. For a closer look at which scribes pass each test, see the HIPAA-compliant AI scribes guide. The best AI medical scribes roundup ranks options by practice size and specialty.
How do I prepare for OCR audits and handle breach notification?
A HIPAA compliance checklist is often among the first documents auditors request. Use the HIPAA Audit Protocol like a working checklist year-round, not a document you pull off the shelf when an audit letter arrives. The protocol (published by HHS) covers the Privacy, Security, and Breach Notification items OCR may review³.
Audited practices must produce:
- Written policies
- Risk analyses
- Training records
- Business associate agreements
- Proof that past issues were fixed
These records serve as proof of ongoing compliance. The HHS Audit Program uses this protocol as the basis for both desk audits and on-site reviews².
Practical preparation comes down to four habits:
- Keep all your compliance records in one searchable place. Auditors ask for specific items. Handing them over quickly shortens the audit and cuts follow-ups.
- Run an internal audit against the OCR protocol once a year. Use it as a gap-check tool.
- Turn on and regularly review audit logs. Audit controls are required under the Security Rule. OCR has cited practices for ignoring their own logs.
- Keep an incident log. Log every suspected event, even the ones that don't trigger formal notice.
Breach notification has its own clock. Any breach of unsecured PHI requires notifying affected individuals within 60 days of discovery⁴. If the breach affects 500 or more individuals total, you must also notify HHS within the same 60 days. If it affects more than 500 residents of a single state or jurisdiction, you must also notify prominent media in that area.
For breaches under 500 individuals, you still owe affected individuals notice within 60 days. HHS reporting for these can be batched annually, due 60 days after the end of the calendar year (in practice, by March 1). Business associates have their own 60-day window to notify you of a breach. Watch out: their discovery date can start your clock for individual notice, so don't assume a fresh 60 days when their notice arrives. The HIPAA compliance checklist should include a short playbook so the first 24 hours after a suspected breach follow a known sequence.
How Commure Scribe approaches HIPAA compliance
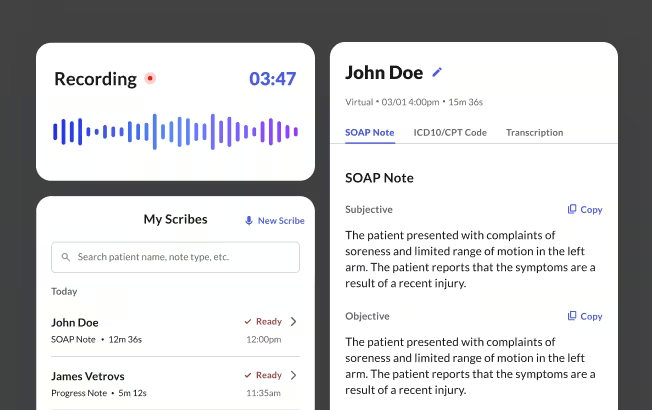
Commure Scribe is an ambient AI documentation tool used by 75,000+ clinicians across 25M+ patient encounters annually. Its HIPAA posture maps directly to the five HIPAA compliance checklist criteria in the section above.
Business associate agreement. Commure Scribe signs a BAA with every customer before the product touches PHI. The BAA binds subcontractors to the same PHI protections.
Encryption and access control. All patient data is encrypted in transit using HTTPS with TLS. Data at rest is encrypted with strong encryption. Audio recordings are stored encrypted. Access is controlled through JWTs, OAuth2, and HMAC-signed URLs.
Data retention and deletion. As of April 2026, Commure Scribe keeps audio active for a set period, then archives it long-term. The archive window is designed to meet HIPAA's six-year minimum. Customers that want a shorter active period can choose to archive after 14 days. Archived audio is locked to HIPAA-trained staff and only pulled on customer request for legal or compliance reasons. Users can delete transcripts and notes on their own, under their contract.
Training data policy. Commure Scribe's terms state that customer audio is not used to train general AI models. Audio is only used to provide and support the service. Third-party data sharing is limited to the subprocessors listed in your contract.
Third-party audit. Commure Scribe holds SOC 2 and other independent security reports, with data stored onshore. Customers can request current reports when evaluating the product.
Disclaimer: This article and the companion checklist are for information and education only. They are not legal advice, and finishing a checklist does not guarantee HIPAA compliance. Talk to qualified legal and compliance counsel for your situation.
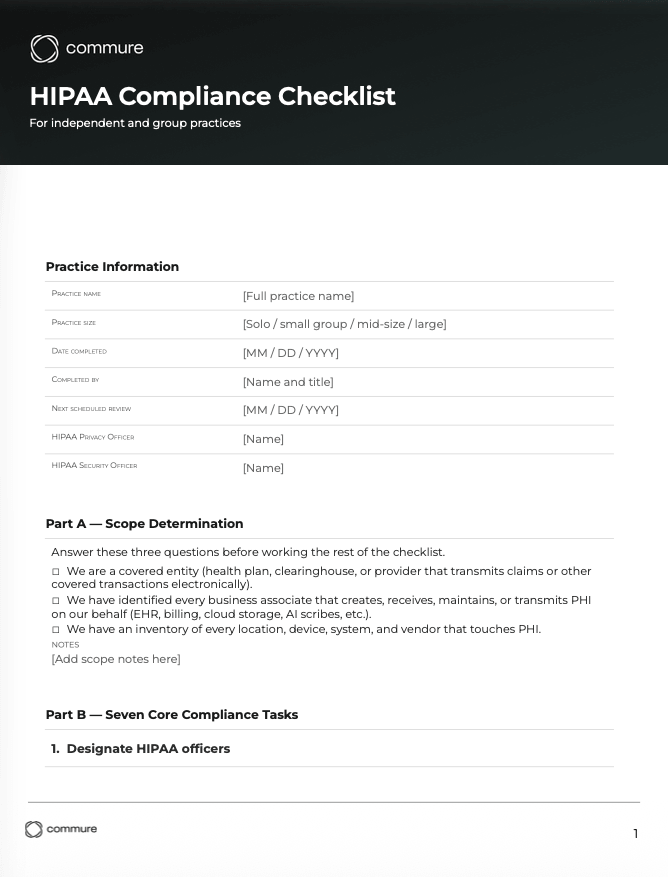
HIPAA Compliance Checklist Template Download
Download a copy of this template
Thank! Your HIPAA Compliance Checklist is ready for you.
Click below to downloa
Frequently Asked Questions
Most HIPAA compliance checklists focus on three core rules: Privacy, Security, and Breach Notification. The Privacy Rule limits who can see or share protected health information. The Security Rule requires safeguards for electronic PHI. The Breach Notification Rule says when and how covered entities must report leaks.
HIPAA requires covered entities to retain required documentation for at least six years. The clock runs from the date of creation or the date it was last in effect, whichever is later. State law or organizational policy may require longer retention for medical records. Retention applies to: policies and procedures, risk analyses, training records, business associate agreements, audit logs, and breach response records.
OCR runs desk audits and on-site reviews using the HIPAA Audit Protocol. The protocol covers the main Privacy, Security, and Breach Notification items OCR may check. Practices have a short window to produce written policies, risk analyses, training records, BAAs, and proof they've fixed past issues. A well-maintained HIPAA compliance checklist shortens that window.
When reviewing an AI scribe for HIPAA, many groups look for five items: a signed BAA when required, Strong encryption in transit and at rest, a clear retention and deletion policy, written limits on data use, including model training, and independent third-party security reports such as SOC 2 Type II.
Every covered entity and business associate can benefit from a structured HIPAA compliance checklist to stay organized. HIPAA doesn't require any specific format. Covered entities include health plans, clearinghouses, and most providers that transmit claims electronically. Business associates include EHR vendors, billing services, cloud storage providers, and AI documentation tools. Any outside party that handles PHI for a covered entity qualifies.
Sources
- American Medical Association. (n.d.). HIPAA: Top tips for physicians. https://www.ama-assn.org/system/files/hipaa-toolkit.pdf
- HHS Office for Civil Rights. (2011). OCR's HIPAA Audit Program. U.S. Department of Health and Human Services. https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/audit/index.html
- HHS Office for Civil Rights. (2018). HIPAA Audit Protocol. U.S. Department of Health and Human Services. https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/audit/protocol/index.html
- HHS Office for Civil Rights. (n.d.). Breach Notification Rule. U.S. Department of Health and Human Services. https://www.hhs.gov/hipaa/for-professionals/breach-notification/index.html
- HHS Office for Civil Rights & Office of the National Coordinator for Health Information Technology. (2010). Guidance on Risk Analysis. U.S. Department of Health and Human Services. https://www.hhs.gov/hipaa/for-professionals/security/guidance/guidance-risk-analysis/index.html
- U.S. Department of Health and Human Services. (2015). HIPAA Guidance Materials. https://www.hhs.gov/hipaa/for-professionals/privacy/guidance/index.html
Try the #1 AI Scribe for Free
No Credit Card Required. Join 20,000 Clinicians.